Do you need help & advice with a Part-Time IT Manager or Business Continuity?
Cyber security and compliance
Many small businesses come to us overwhelmed by requirements set out by their industry, insurers, or customers.
We can help ensure you exceed these risk assessment standards without spending a lot of time getting to grips with the terminology.
We focus on the basics, get this done right and a lot of cyber issues vaporise.
Many people are so caught up in technobabble, marketing noise, and compliance terminology they fail to prioritise and organise the risk and compliance simply becomes a tick box exercise which in our experience means you are very unlikely to actually comply with the requirements.
If you need a vCISO or just getting cyber essentials, our framework will allow you to:
- Reduce your risk
- Develop a CyberSecurity posture aligned to your risk appetite (aka: Educate the company directors that a breach could cost upwards of 6-7 figures to recover from. Plus the ongoing reputational damage.
- Enable you to stay ahead of hackers and compliance requirements rather than lie that you meet their requirement leading to legal issues later on.
While we want to make sure to meet the regulatory requirements. most important is we are improving the risk posture, have a proper incident response plan and are continuous monitoring for risks in the IT systems.
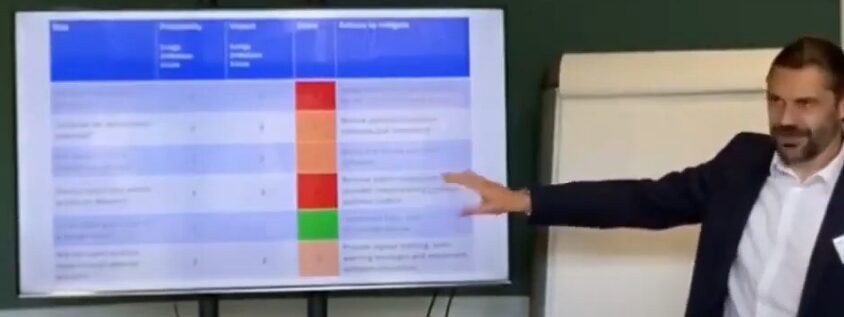
We have built our own internal process (based on the NIST industry standard) to help small business leaders understand the cybersecurity risks in plain English. Better understanding of the cyber threats will mean that improving the security posture is much easier as leaders understand the reputation damage, financial costs, and crippling loss of productivity that can result from a breach. Security issues are no longer an IT problem but a risk business owners, board members, and every person in your organisation must understand and control
How does cybersecurity compliance work?
Meeting and exceeding compliance standards can be an expensive and overwhelming undertaking for an SME.
Often treated as a tick box exercise rather than an opportunity to reduce business risk and improve cybersecurity posture.
We take cybersecurity seriously and we have simple cyber and fractional leadership packages which not only help you meet or exceed the assessment requirements but far more importantly actually significantly reduce the chances of business failure due to a cyber attack.
Many business leaders are incredibly naïve to cyber risks so we can help you keep the lights on.
For very small businesses, we offer a simple cyber package which is constantly adapting to new risks. For larger businesses, we can provide quarterly cyber strategy meetings to ensure your business is rapidly improving to keep up with the risks. Many businesses and standards are 3-5 years behind so extensive work is needed for the most basic security controls.
Unfortunately, usually, we are contacted after a breach, which is a very expensive learning exercise.
If you think simply having a firewall and antivirus is sufficient let us be clear it absolutely isn’t!
That was ok a decade ago but budgets for cybersecurity now are close to those for IT support. We can make sure your training, leadership and standards such as cyber essentials, NIS, NIST, PCI, ISO etc. are met and that company directors are confident they understand the risks they are managing.
We can work with your IT team, provide specialist cyber vCISO’s and work with our partners to get you the best service. By controlling the risks first instead of selling fancy buzzwords or boxes we are confident you are in safe hands.
Most business are not aware that third-party vendors are the biggest cause of breaches, so it’s vitally important to have processes in place to validate their process and risk appetite as well as your own
Regulatory Requirements & the world of acronyms
If you are in regulated industry or work for government organisations you will need to comply with various regulatory standards. Financial Institutions, Accountants and legal advisers all need to meet strict compliance requirement standards for example
GDPR
The General Data Protection Regulation (GDPR) is a crucial law that aims to protect the personal data and privacy rights of individuals in the European Union (EU) and European Economic Area (EEA). It provides a comprehensive legal framework for companies and organizations to follow when collecting, storing, and processing personal data. With its clear guidelines, the GDPR ensures that individuals have control over their data and can make informed decisions about how it is used.
Under the GDPR, businesses are required to provide transparent terms and conditions regarding their data collection practices. This means that individuals must be fully aware of what data is being collected, why it is being collected, how it will be used, and if it will be shared with third parties. Additionally, individuals have the right to access their personal data held by companies and can request changes or deletion of their information. Companies are obligated to protect this data from unauthorized access or breaches and must notify individuals if such incidents occur.
The GDPR puts a strong emphasis on obtaining explicit consent from individuals before processing their personal information. Consent must be freely given, specific, informed, and unambiguous. By making consent a definitive criteria for businesses to process personal data, the GDPR ensures that individuals have control over who has access to their information.
The world of compliance cybersecurity standards
While a large business may have a detailed governance, risk and compliance (GRC) process, small businesses are easily overwhelmed by all the compliance standards
NIST, NIS2, SOC2, GDPR, ISO27001, CMMC, HIPPA, PCI-DSS, FISMA, Cyber Essentials, Cyber Essentials Plus
We take the more sensible and cost effective Risk Management approach:
- What do you need to do right now that will reduce your risks of a cyber attack?
- What do you need to do in the future to remain compliant with all the compliance standards?
Unfortunately, many businesses are doing this backwards – realise they need to meet a standard and then panic purchasing a “solution” to get through the standard – we have seen several cases now where businesses clearly do not meet the standards they have certified. They are sold a buzzword heavy solution which may look nice, but ultimately will not prevent a breach, you can buy the most expensive burglar alarm but if you leave your windows and doors wide open and go out it will not help! My advice is, leave the light on when you go out first, then maybe later on we will buy the expensive alarm system.
- NIST (National Institute of Standards and Technology): NIST provides a framework for improving cybersecurity in organizations by outlining best practices, guidelines, and standards. More information can be found on the NIST website: https://www.nist.gov/cyberframework
- NIS2 (Network and Information Systems Directive): NIS2 is a European Union directive focused on improving the cybersecurity of essential services and digital service providers. More information can be found on the European Commission website: https://ec.europa.eu/digital-single-market/en/network-and-information-security-nis-directive
- SOC2 (Service Organization Control 2): SOC2 is a framework for managing customer data based on five trust service criteria: security, availability, processing integrity, confidentiality, and privacy. More information can be found on the American Institute of CPAs website: https://www.aicpa.org/interestareas/frc/assuranceadvisoryservices/sorhome.html
- GDPR (General Data Protection Regulation): GDPR is a regulation in the EU focused on data protection and privacy for all individuals within the EU and the European Economic Area. More information can be found on the European Commission website: https://ec.europa.eu/info/law/law-topic/data-protection_en
- ISO27001: ISO27001 is an international standard for information security management systems (ISMS) that helps organizations manage the security of their information assets. More information can be found on the International Organization for Standardization website: https://www.iso.org/isoiec-27001-information-security.html
- CMMC (Cybersecurity Maturity Model Certification): CMMC is a standard developed by the US Department of Defense to assess and enhance the cybersecurity posture of defense contractors. More information can be found on the Office of the Under Secretary of Defense for Acquisition and Sustainment website: https://www.acq.osd.mil/cmmc/
- HIPAA (Health Insurance Portability and Accountability Act): HIPAA sets the standard for protecting sensitive patient data in the healthcare industry. More information can be found on the U.S. Department of Health and Human Services website: https://www.hhs.gov/hipaa/index.html
- PCI-DSS (Payment Card Industry Data Security Standard): PCI-DSS is a set of security standards designed to ensure that all companies that accept, process, store, or transmit credit card information maintain a secure environment. More information can be found on the PCI Security Standards Council website: https://www.pcisecuritystandards.org/
- FISMA (Federal Information Security Management Act): FISMA provides guidelines and standards for federal agencies to secure their information systems and data. More information can be found on the National Institute of Standards and Technology website: https://csrc.nist.gov/standards/fisma
- Cyber Essentials and Cyber Essentials Plus: Cyber Essentials is a UK government-backed certification scheme designed to help organizations protect against common cyber threats. More information can be found on the National Cyber Security Centre website: https://www.cyberessentials.ncsc.gov.uk/
- GRC (Governance, Risk, and Compliance): GRC is a strategy for managing an organization’s overall governance, risk management, and compliance with regulations. More information can be found on Gartner’s website: https://www.gartner.com/en/information-technology/glossary/grc-governance-risk-and-compliance